The shadowed web whispers secrets, a labyrinth of encrypted connections and anonymous identities. Darknet links, similar to cryptic ciphers, lead to hidden realms where the ordinary rules fail to apply. Here,we on a journey into these uncharted territories, unveiling the mysteries that hide within. Prepare to encounter a world of both intrigue, where the line between fantasy blurs.
- Dive into the secrets of the Deep Web
- Unmask the anonymous identities that inhabit these digital shadows
- Translate the intricate passphrases that protect this secret knowledge
Navigating the Labyrinth: A Guide to Onion Links
The world of onion links can be like a complex labyrinth, full of levels. These hidden pathways, often used for secure communication, can transport to secret information. But with the right understanding, navigating this digital puzzle is achievable. A good starting point is understanding how onion links are structured. They typically initiate with the URL "onion" or ".onion". This points to a connection to the Tor network, which shields your onionlinks traffic and hides your location.
From there, each onion link acts like a layer of an onion, channeling you to a new server. This recursive approach makes it hard for anyone to monitor your activity.
- Keep in mind onion links can be risky content, so proceed with caution.
Beyond the Surface: Exploring Hidden Networks Through Onion Links
The darknet is a vast and mysterious landscape. While most users only explore the surface, hidden communities exist beneath the surface, accessible through hidden links. These links lead to a world of secrecy, where users can connect freely without concern of tracking.
- Exploring these hidden networks can be unpredictable, as it's possible to stumble upon undesirable content or engage with untrustworthy individuals.
- Nevertheless, for those who seek anonymity, Onion links offer a intriguing opportunity to enter hidden communities.
It's important to practice extreme caution when exploring these networks, and to always emphasize your digital protection.
Secure Communication: The Power and Peril of Onion Links
Onion links, also known as/referred to as/dubbed deep web entries/connections/passages, present a fascinating/intriguing/complex paradox in the realm of online communication/interaction/exchange. They offer a veil/shield/layer of anonymity/obscurity/privacy by routing traffic/data/information through multiple servers/nodes/layers, masking/concealing/hiding the user's true identity/location/IP address. This inherent security/protection/encryption makes them attractive/appealing/useful for whistleblowers, activists, and those seeking to engage in/participate in/conduct sensitive online activities. However, this same anonymity/obscurity/privacy can also foster/breed/encourage illicit behavior/activities/transactions. The dark web, often accessed via onion links, has become a haven/platform/conduit for cybercrime/illegal trade/malicious activity, posing a significant/serious/growing threat to global security/safety/stability. Navigating the world of onion links requires a keen/critical/discerning eye and a deep understanding/awareness/knowledge of both their potential benefits and inherent risks.
Unmasking the Truth: Onion Links and Their Deceptive Nature
Beneath their seemingly innocuous exterior, onion links mask a sinister landscape. These web addresses, often disguised as legitimate connections, can lead users down a rabbit hole of harmful content. From compromising personal information to spreading viruses, the dangers lurking behind onion links are grave. Be cautious when encountering these cryptic addresses, and always verify their legitimacy before clicking.
Here's a list of potential threats associated with onion links:
- Cyberattacks: Onion links can be used to launch attacks on your computer or network, stealing sensitive data such as passwords, credit card information, and personal files.
- Virus Infections: Clicking on a malicious onion link can download harmful software onto your device, leading to system malfunction and potential data loss.
- Deceptive Links: Onion links often disguise themselves as legitimate websites, tricking users into revealing personal information through bogus login pages or forms.
Stay safe online by educating yourself about the risks associated with onion links and practicing safe browsing habits. Always be skeptical of suspicious links, verify website authenticity, and keep your software up to date to protect yourself from potential harm.
Piercing the Veil of Anonymous Browsing
In the digital age, anonymity can be a shield. Users desire secrecy online for a range of reasons, from protecting sensitive data to communicating without fear. However, this desire for anonymity often clashes with the increasing demand for transparency and accountability in the online world. The onion metaphor, frequently employed, aptly depicts the layered nature of anonymous browsing, where multiple methods work together to obscure a user's true identity and location.
Despite this, the quest for anonymity is not without its difficulties. Law enforcement agencies, cybersecurity experts, and even tech companies themselves are constantly exploring ways to penetrate anonymous users and address the potential for online crime. The battle between anonymity and transparency is a evolving landscape, presenting crucial questions about individual rights in the digital age.
 Emilio Estevez Then & Now!
Emilio Estevez Then & Now! Rick Moranis Then & Now!
Rick Moranis Then & Now!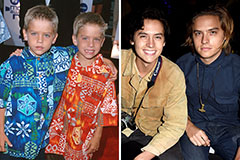 Dylan and Cole Sprouse Then & Now!
Dylan and Cole Sprouse Then & Now! Joshua Jackson Then & Now!
Joshua Jackson Then & Now! Pierce Brosnan Then & Now!
Pierce Brosnan Then & Now!